This post provides step-by-step instructions for setting up single sign-on (SSO) from Salesforce to Sage Intacct.
Note that the instructions and screenshots below are using Intacct’s new “Action UI”. To see instructions in the legacy UI, see this article.
Prerequisites
- Sage Intacct account with system administrator access. If you are a current Intacct customer, you can purchase an Intacct sandbox environment. If you are working with an implementation partner, you can usually get access to a temporary “copy company” environment via your implementation partner.
- Salesforce org with identify features (developer or enterprise and up) with system administrator access. Sign up for a free developer edition org here.
Step 1: Set up My Domain in Salesforce
The My Domain feature creates a custom subdomain for your org and is required to use Salesforce as an identity provider. Go to Setup -> My Domain, enter a name for your subdomain and click “Check Availability”. Once you get a confirmation that the subdomain is available, click “Register Domain”. Salesforce will send you an email when the custom domain has been registered.
Click the link in the email and log in using your new domain. Navigate back to the My Domain page in setup. Click the “Deploy to Users” button.
Step 2: Enable Salesforce as an Identity Provider
You’ll need a self-signed or commercially signed certificate in order to enable Salesforce as an identity provider. If you don’t already have a certificate in the Salesforce org, you can quickly create one by going to Setup -> Security -> Certificate and Key Management. Click the “Create Self-Signed Certificate. Enter a descriptive name for the label and the unique name will be populated automatically. Click the “Save” button.
Now we can enable the Salesforce org to be an identity provider. Go to Setup -> Identity -> Identity Provider. Click “Enable Identity Provider”. Select the certificate you just created, or an existing one.
Step 3: Create a Connected App in Salesforce
The connected app is going to store information about Sage Intacct and is also going to be used to create the tile in the App Launcher so that users can quickly launch Sage Intacct from Salesforce.
Navigate to App Manager in Setup and click “New Connected App” in the top right of the page. Use the following values
- Connected App Name: Sage Intacct
- API Name: Sage_Intacct
- Contact Email: (any email address)
- Logo Image URL: (click “Upload logo image” and upload an image file that is 125×125 pixels – this will appear in the app launcher tile)
- Enable SAML: true
- Entity Id: (available from Intacct Support Community; it will look something like “https://saml.intacct.com”)
- ACS URL: (available from Intacct Support Community; it will look something like “https://www.intacct.com/ia/acct/sso_response.phtml”)
- Subject Type: Federation ID
- Name ID Format: urn:oasis:names:tc:SAML:1.1:nameid-format:emailAddress
- Issuer: this should be your custom Salesforce domain: https://<custom-domain>.my.salesforce.com (may also look like this if you are using a developer edition org: https://<custom-domain>.dev-ed.my.salesforce.com)
- IdP Certificate (Keep default value)
Click the “Save” button.
Next we need to give users access to the connected app. Navigate to Manage Connected Apps. Click the “Sage Intacct” app to open the detail page of the connected app. Click Manage Profiles and add the System Administrator profile.
Now we need to add several Custom Attributes that are required by Sage Intacct. Create a custom field on the User object to store the Intacct User ID.
Click the “New” button in the Custom Attributes section of the connected app detail page. Add the following
- Attribute key = emailAddress, Attribute value = $User.Email
- Attribute key = Company Name, Attribute value = (get from your Intacct environment: Company -> Company information -> ID field)
- Attribute key = name, Attribute value = $User.Intacct_User_ID__c (use the API name for the custom field you created on the User object to store this value)
Finally, we need to set the Start URL for the connected app. Copy the IdP-initiated login URL in the SAML Login Information section of the connected app detail page. Click the “Edit Policies” button. Paste the IdP-initiated URL into the Start URL field and click the “Save” button.
Step 4: Configure SSO Settings in Sage Intacct
Download the Certificate from Salesforce
First, download the certificate you used when enabling Salesforce as an identity provider by navigating to Setup -> Security -> Certificate and Key Management. Click the name of the certificate and then the “Download Certificate” button.
The file downloaded from Salesforce is Base64-encoded with a .crt extension and Sage Intacct accepts the text of the certificate. You can view the text of the public key with the following OpenSSL command in a terminal
openssl x509 -in certificateName.crt -text
From the terminal output, copy the content of your Salesforce certificate between the “—–BEGIN CERTIFICATE—–” and “—–END CERTIFICATE—–” labels.
Update SSO Settings in Sage Intacct
Log into Sage Intacct and navigate to the Company navigation section. Select the Setup tab and click the “Company” page. Select the Security tab and click the “Edit” in the top right corner of the page.
Scroll down to the Single sign-on (SSO) section and check the box “Enable single sign-on” and enter the following values:
- SSO Identity Provider Type: SAML 2.0
- SSO Issuer URL: (this should be the same as the Entity ID value in the Salesforce connected app, e.g. “https://saml.intacct.com”)
- SSO Login URL: (enter the value of the “SP-Initiated Redirect Endpoint from the Connected App created in Step 3)
- SSO Certificate: (paste the value of the certificate you copied from your terminal)
Click “Save”.

Step 6: Test the Single Sign-on Flow
Create SSO User
In the Company -> Admin -> Users page in Sage Intacct, create a new user to test the SSO authentication flow. On the “User information” tab enter values for the following fields: User ID, Last Name, First Name and Email Address.
Note the values you enter in the Email Address and User ID fields for the Intacct user record. On the “Single sign on” tab, check the box “Enable single sign-on for this user” and enter the value you copied from the Email Address field into the “Federated SSO user id” field. Click “Save” and confirm.
Finally, navigate to the user record in the Salesforce org that you are going to use to test single sign-on. This user should be a system administrator, because that is the only profile we granted access to in the connected app. Click the “Edit” button and enter the value of the Email Address you used when creating the new user in Sage Intacct into the “Federation ID” field and paste the value of the Intacct User ID into the custom field you created on the User object you created to store this value. Save the user record.
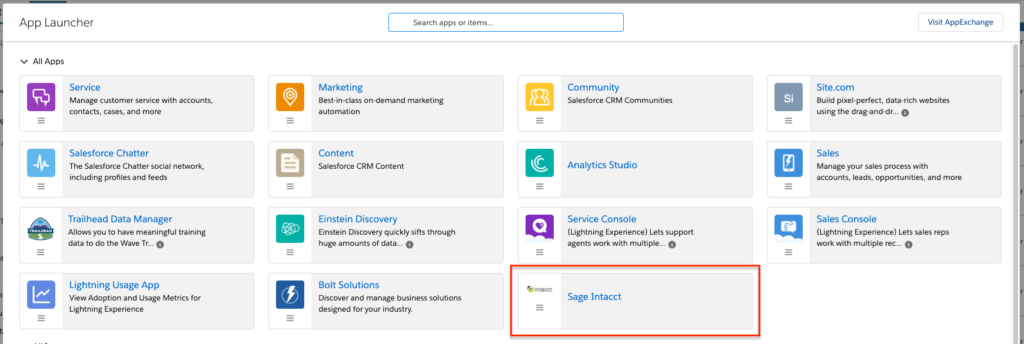
Test IdP-initiated Login with the Salesforce App Launcher
Open the App Launcher. You should see a tile for your Sage Intacct connected app. Click the tile and Sage Intacct should open and you should be logged in automatically.
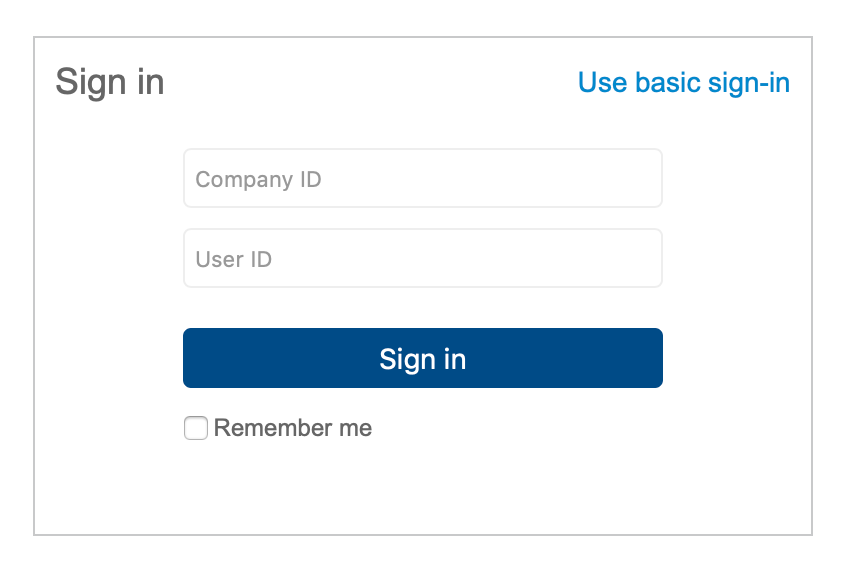
Test SP-initiated Login
Navigate to https://www.intacct.com/ia/acct/login.phtml. Click the “Use single sign-on” link. Enter your Company ID and User ID and click the “Sign in” button. If you are already logged into Salesforce, you should be authenticated directly into Sage Intacct.
Resources
- Salesforce documentation: App Launcher
- Intacct documentation: Setting up Single Sign On
- Intacct documentation: Troubleshooting SSO





