Tableau is one of the most popular data analysis and visualization tools on the market. Tableau Foundation provides generous donations to nonprofits. Tableau Online is a cloud solution for hosting and sharing Tableau visualizations. This post provides step-by-step instructions for setting up single sign-on (SSO) from Salesforce to Tableau Online.
Prerequisites
- Tableau Online account with system administrator access. Sign up for a trial here.
- Salesforce org with identify features (developer or enterprise and up) with system administrator access. Sign up for a free developer edition org here.
Step 1: Set up My Domain in Salesforce
The My Domain feature creates a custom subdomain for your org and is required to use Salesforce as an identity provider. Go to Setup -> My Domain, enter a name for your subdomain and click “Check Availability”. Once you get a confirmation that the subdomain is available, click “Register Domain”. Salesforce will send you an email when the custom domain has been registered.
Click the link in the email and log in using your new domain. Navigate back to the My Domain page in setup. Click the “Deploy to Users” button.
Step 2: Enable Salesforce an Identity Provider
You’ll need a self-signed or commercially signed certificate in order to enable Salesforce as an identity provider. If you don’t already have a certificate in the Salesforce org, you can quickly create one by going to Setup -> Security -> Certificate and Key Management. Click the “Create Self-Signed Certificate. Enter a descriptive name for the label and the unique name will be populated automatically. Click the “Save” button.
Now we can enable the Salesforce org to be an identity provider. Go to Setup -> Identity -> Identity Provider. Click “Enable Identity Provider”. Select the certificate you just created, or an existing one.
Step 2: Enable SAML in Tableau Online
Log into Tableau Online and (1) click on the “Settings” tab, and then (2) the “Authentication” sub-tab. Check the box (3) “Enable an additional authentication method” and (4) select the SAML option. Click on the (5) “Edit Connection…” link to expand the SAML settings section.
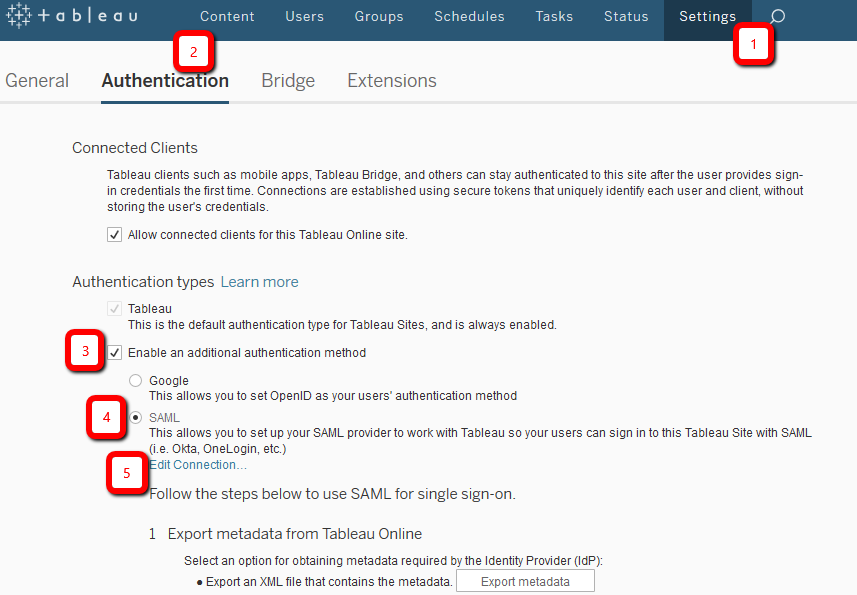
You’ll use the information in this expanded section in the next step.
Step 3: Create a Connected App in Salesforce
The connected app is going to store information about Tableau Online and is also going to be used to create the tile in App Launcher so that users can quickly launch Tableau Online from Salesforce.
Navigate to App Manager in Setup and click “New Connected App” in the top right of the page. Use the following values
- Connected App Name: Tableau Online
- API Name: Tableau_Online
- Contact Email: (any email address)
- Logo Image URL: (click “Upload logo image” and upload an image file that is 125×125 pixels – this will appear in the app launcher tile)
- Enable SAML: true
- Entity Id: (enter the value from the “Tableau Online Entity ID” field from the previous step)
- ACS URL: (enter the value from the “Assertion Consumer Service URL” field from the previous step)
- Subject Type: Federation ID
- Name ID Format: (keep default value)
- Issuer: this should be your custom Salesforce domain: https://<custom-domain>.my.salesforce.com (may also look like this if you are using a developer edition org: https://<custom-domain>.dev-ed.my.salesforce.com)
- IdP Certificate (Keep default value)
Click the “Save” button.
Next we need to give users access to the connected app. Navigate to Manage Connected Apps. Click the “Tableau Online” app to open the detail page of the connected app. Click Manage Profiles and add the System Administrator profile.
Finally, we need to set the Start URL for the connected app. Copy the IdP-initiated login URL in the SAML Login Information section of the connected app detail page. Click the “Edit Policies” button. Paste the IdP-initiated URL into the Start URL field and click the “Save” button.
Step 4: Configure SAML Settings in Tableau Online
First download the connected app metadata in Salesforce. From the Tableau Online connected app detail page click the “Download Metadata” button.
Navigate to the Authentication sub-tab in Tableau Online and expand the SAML settings section. Find section “4 – Import metadata into Tableau Online”. Click the “Browse…” button and select the file that you just downloaded from the Salesforce connected app. Click the “Apply” button.
In the “Match attributes” section leave the default mapping of Email -> NameID, First name -> FirstName, Last name -> LastName.
Leave the default setting for Embedding options.
In the Manage users section, click the “Add users” link. In the popup select the option to add users for salesforce.com (SAML) authentication. Enter an email address that is different from the one that you used to log into Tableau Online and click the “Add Users” button.
Finally navigate to the user record in the Salesforce org that you are going to use to test single sign-on. This user should be a system administrator, because that is the only profile we granted access to in the connected app. Click the “Edit” button and enter the email address you used when creating the new user in Tableau Online into the “Federation ID” field. Save the user record.
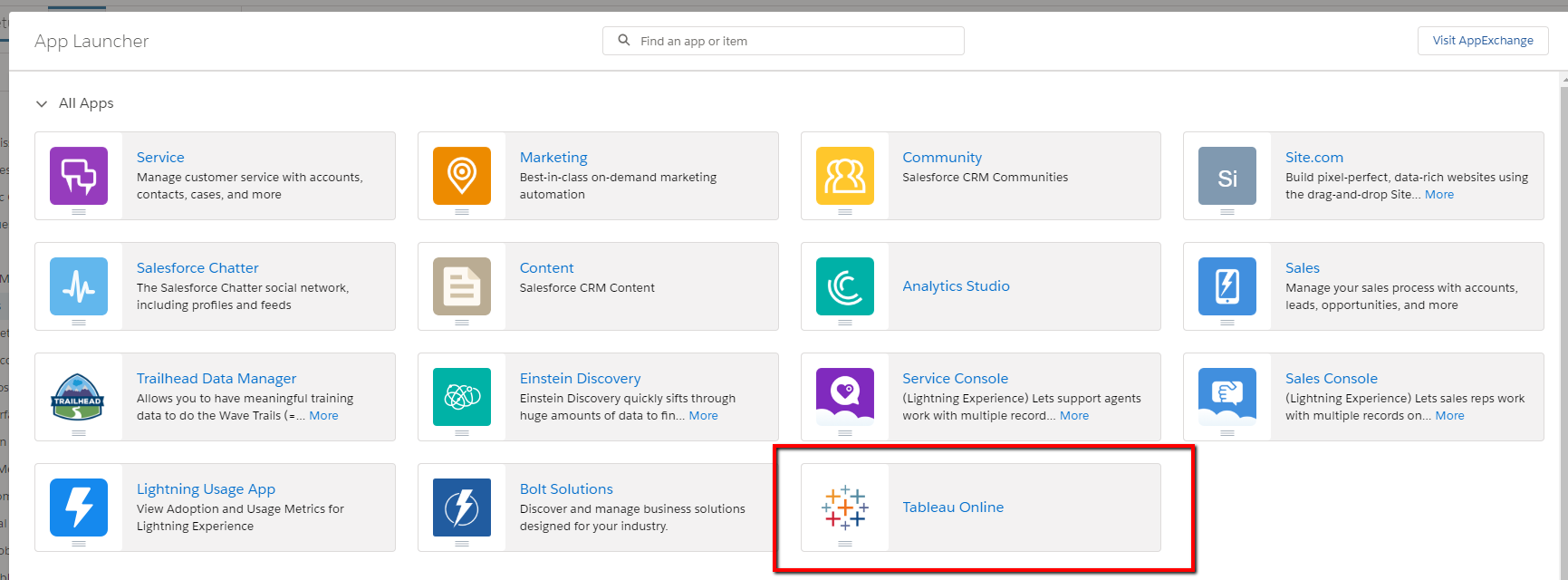
Step 5: Test the Connected App from App Launcher
Open the App Launcher. You should see a tile for your Tableau Online connected app. Click the tile and Tableau Online should open and you should be logged in automatically. If you click on the profile icon and then “My Account Settings” you will see that you are logged in as the user you created while configuring Tableau Online SAML settings.
Resources
Tableau documentation: SAML and Identity Provider Requirements for Tableau Online
Tableau documentation: Enable SAML Authentication on a Tableau Online Site
Salesforce documentation: App Launcher






This is the best documentation on the subject i have seen to date. Thank you.
Very useful article.
The subject type in Step 3 can be set to be ‘User Id’ when the Users don;t have a Federation Id
Is there any reason we couldn’t follow similar steps for Tableau Server?
Hi Arik,
I only tested with Tableau Online, but according to Tableau’s documentation, SAML is supported with Tableau Server as well: https://onlinehelp.tableau.com/current/server/en-us/saml.htm
Thanks for the excellent documentation!
I did discover that I had to check the “Authenticate using an inline frame (less secure; not supported by all IdPs)” option in the “Embedding options” section in Tableau in order to remove a step where the user had to click a button before the visualization would appear.
Not sure it’ll work in all cases, but wanted to drop it here in case others run into it.
Well done, well done! Most useful blog ive read on this. Most articles do not consider authorization – which is the one of the most important parts of a production ussage.
Thanks!
Hi,
I followed all the instructions in the article, and despite that, in the last step by clicking on Tableau Online from app launcher, it go to tableau sso url but i need to put my email and password to login.
can u please help me?
After setting up everything as mentioned above, I am being redirected to Salesforce Classic and getting the following error. “Insufficient Privileges
You do not have the level of access necessary to perform the operation you requested. Please contact the owner of the record or your administrator if access is necessary. For more information, see Insufficient Privileges Errors.” Can any one guide me please?